Trusted by 2,500+ Security Operators
The Unified Intelligence Powerhouse_
Consolidate your toolkit. Scrapers, Scanners, and Dumpers in one place.
Accelerate your workflow. Automated engine synchronization from day one.
Master the operational flow. Move from raw dorks to full dumps effortlessly.
Operational
Efficiency
Dork Parser
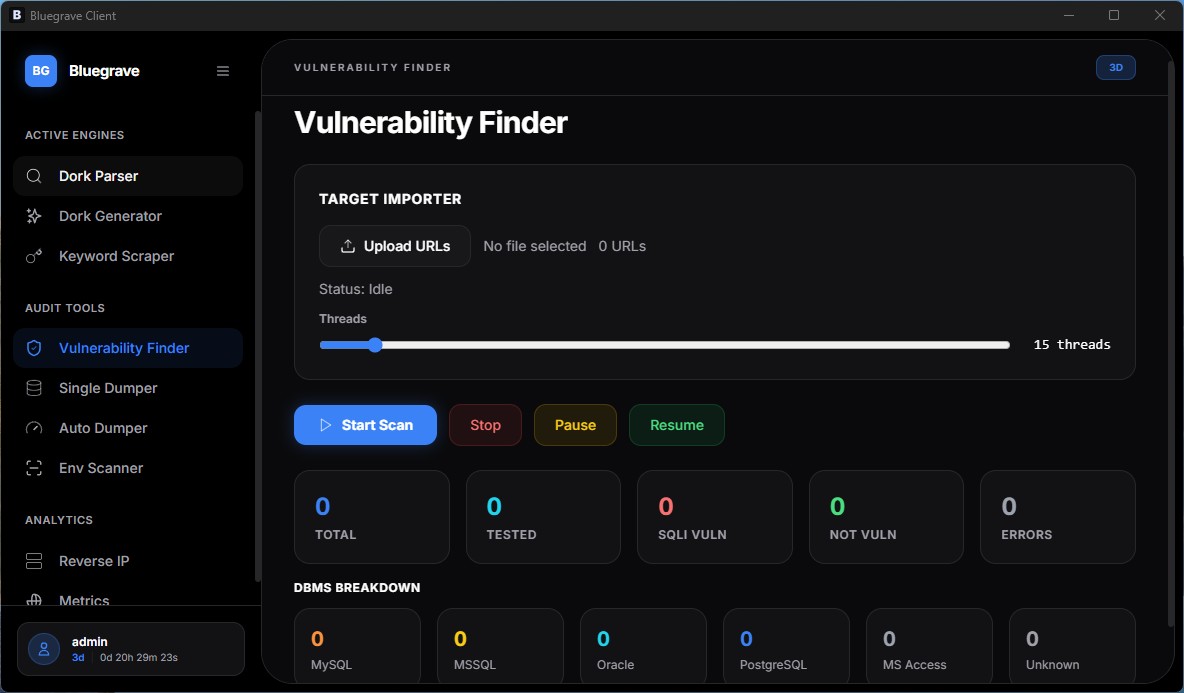
Scanner
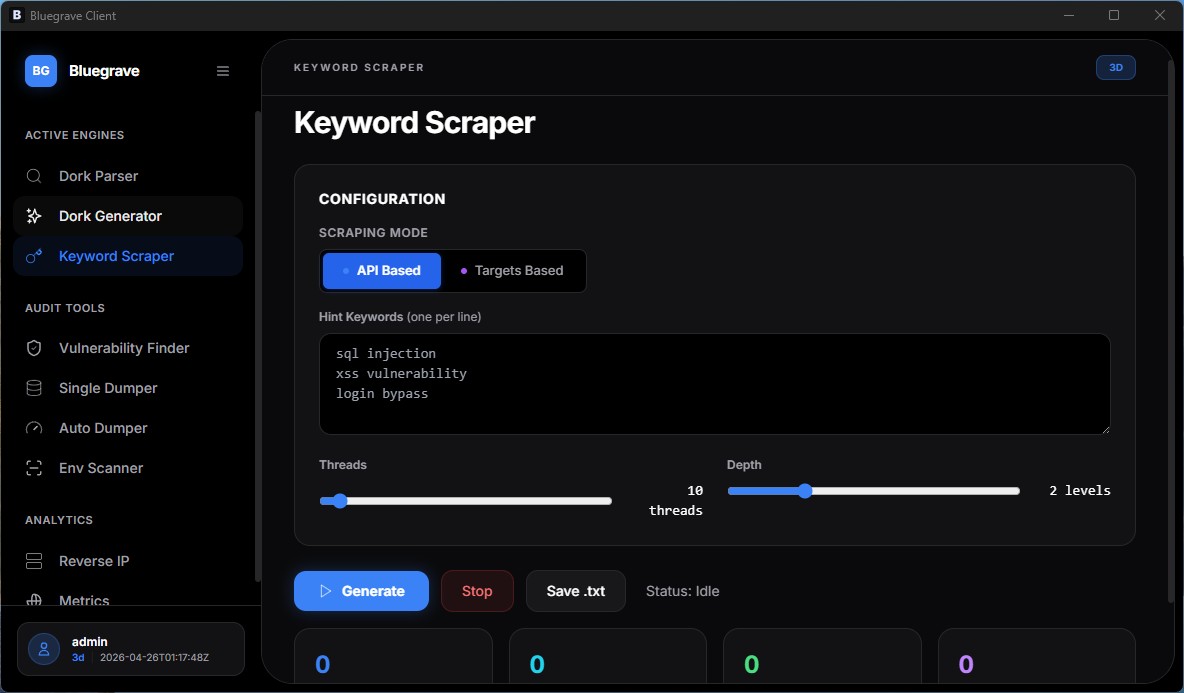
Scraper
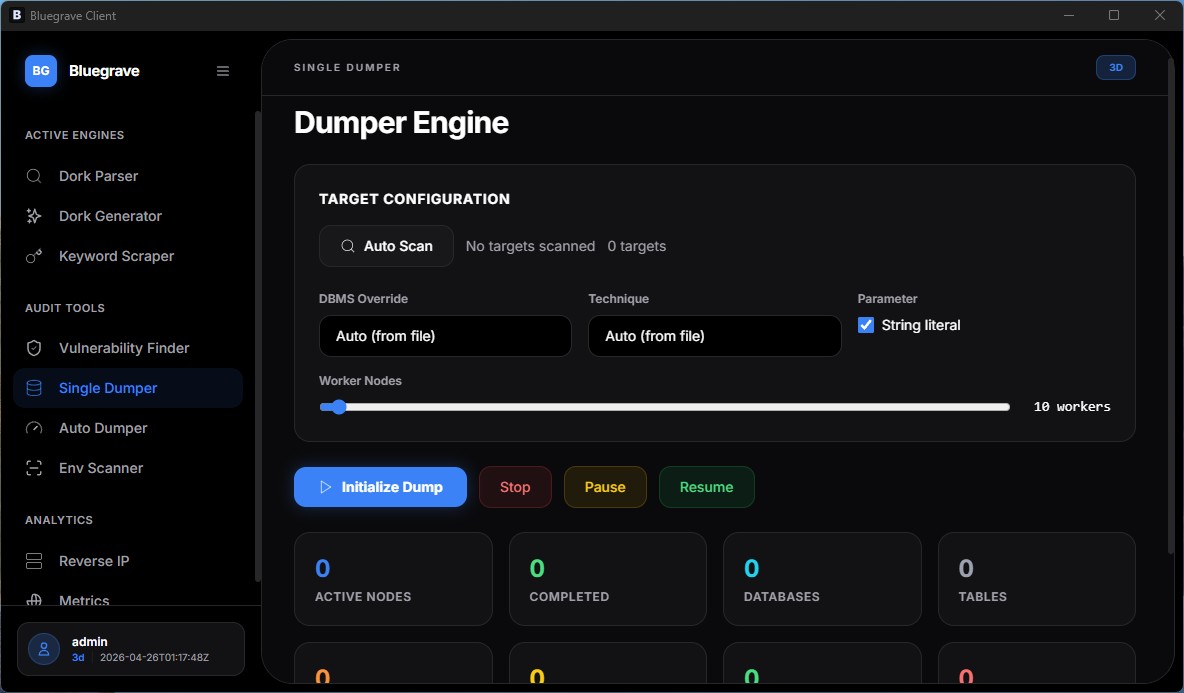
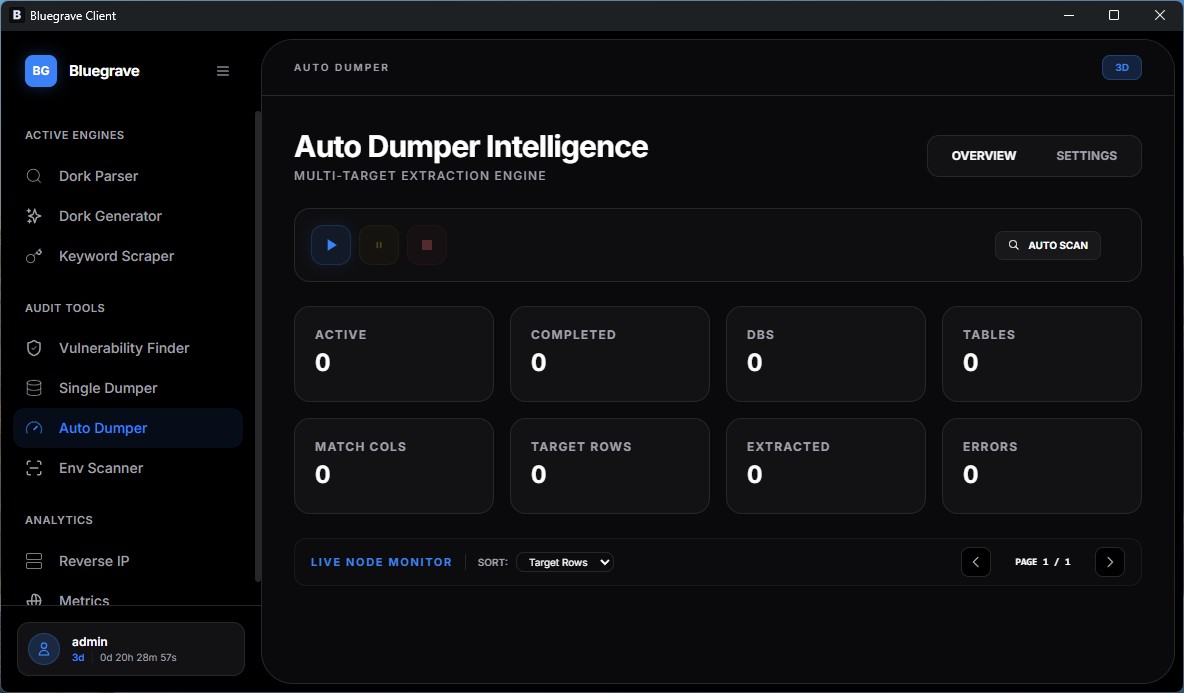
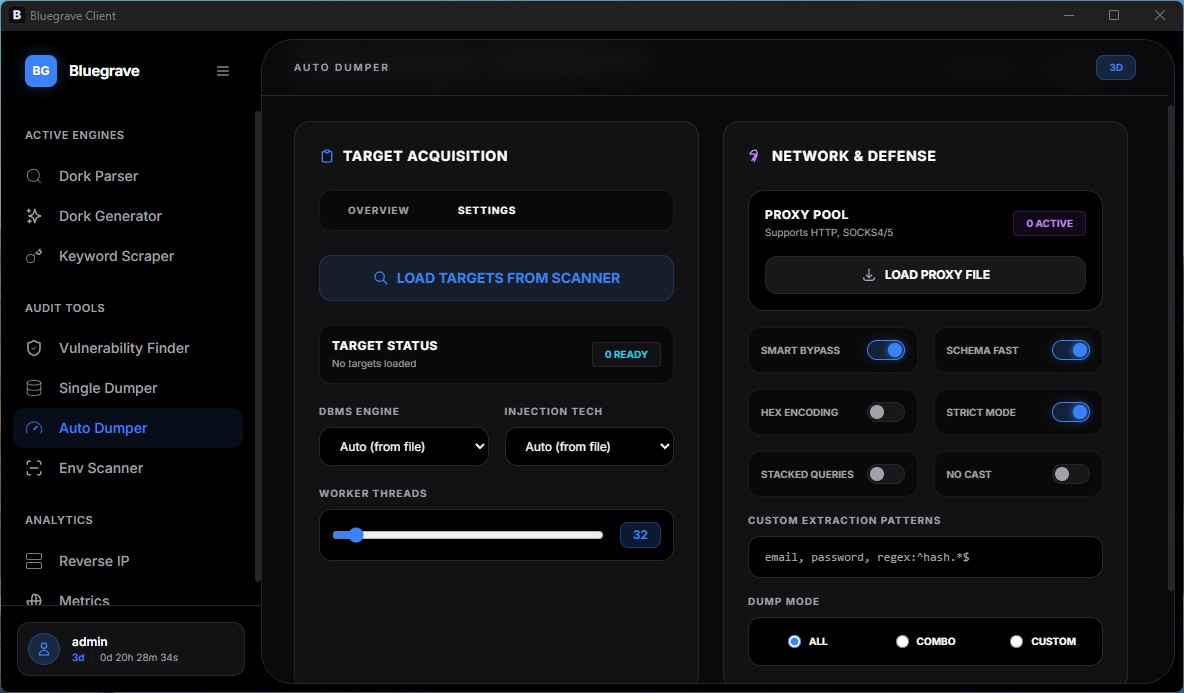
Auto Dumper
DB Explorer
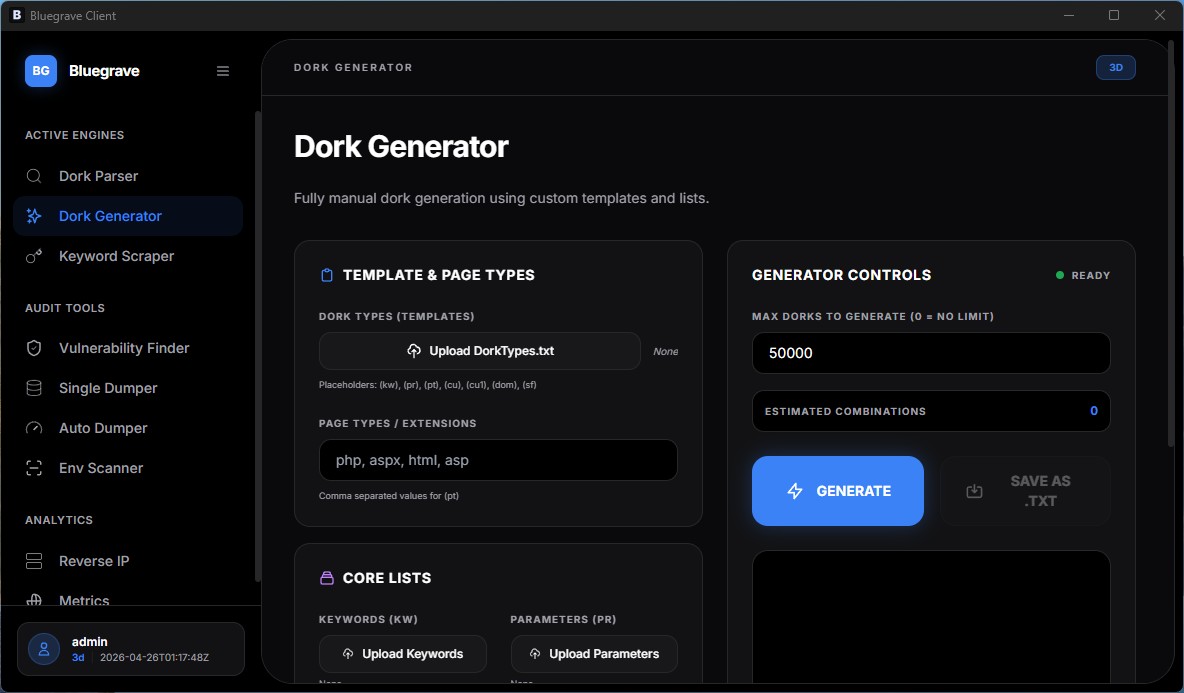
Dork Generator
Env Scanner
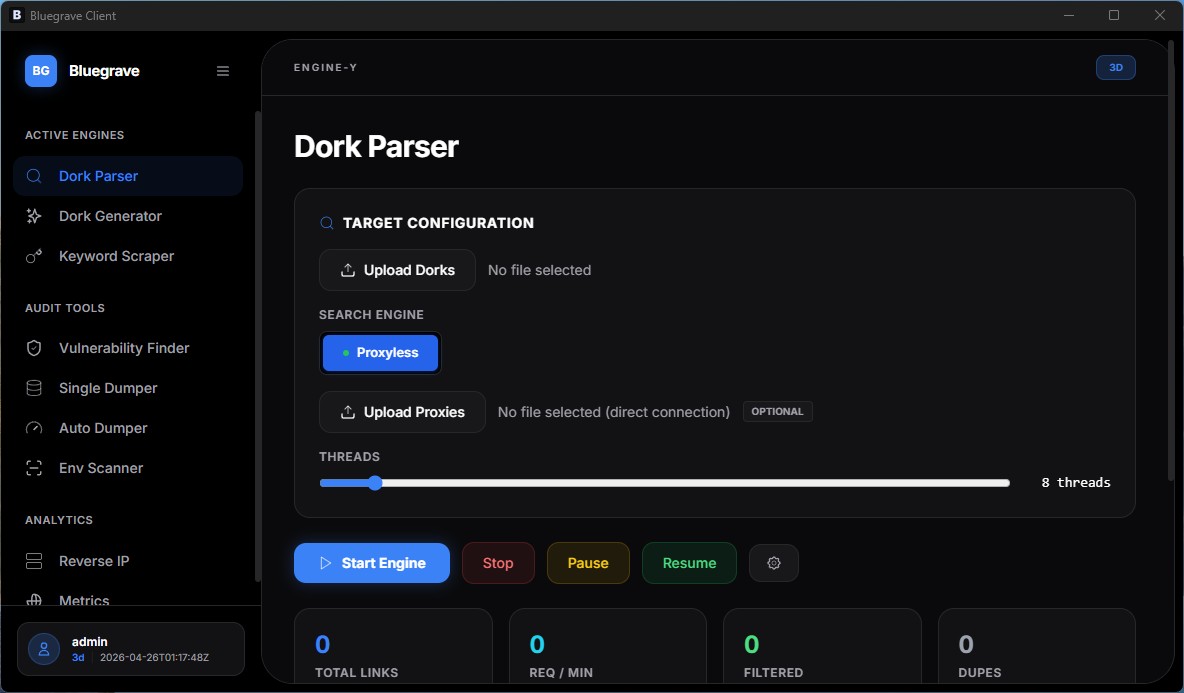
LIVE PERFORMANCE
1.4M REQ/MIN
Powerful tools for every task
Your complete pentesting toolkit, fully automated and synchronized across every stage of the audit.